Understanding Split Tunneling in VPNs
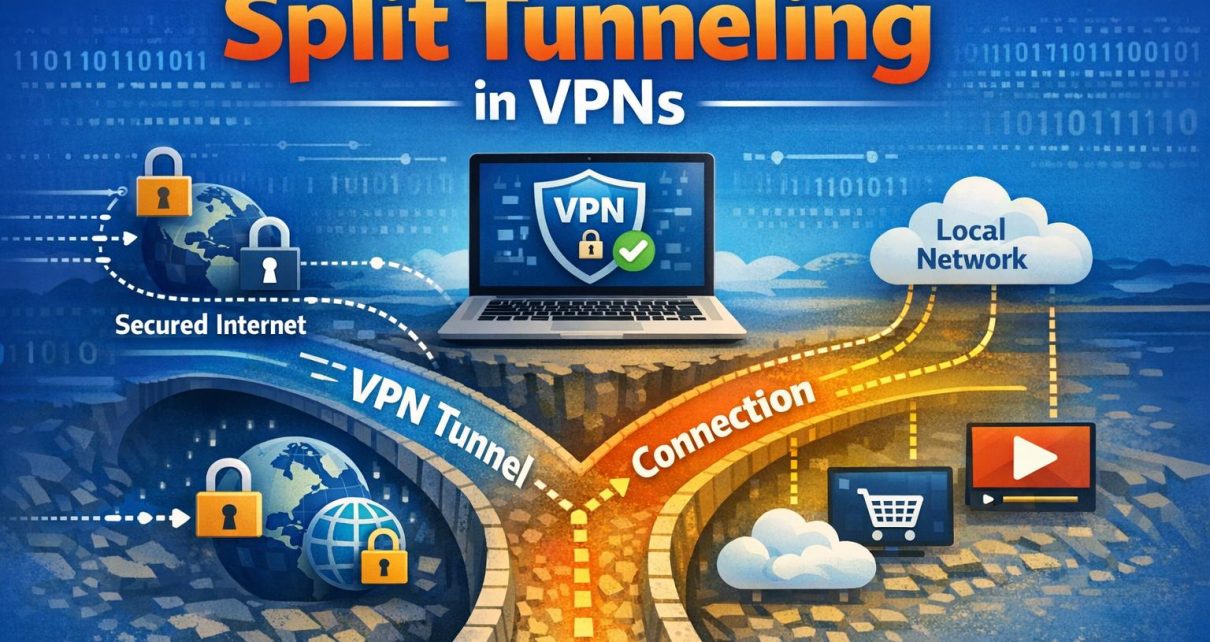
Split tunneling is a feature provided by Virtual Private Networks (VPNs) that allows users to route specific portions of their internet traffic through an encrypted VPN tunnel while allowing other traffic to pass directly through their regular internet connection. This selective routing approach introduces flexibility in how network traffic is managed, offering a balance between security, performance, and accessibility. As internet usage continues to diversify across work, entertainment, and communication, split tunneling has become an increasingly relevant feature for both individuals and organizations.
How Does Split Tunneling Work?
Under standard VPN operation, all outgoing and incoming traffic is routed through a secure, encrypted tunnel to a remote server operated by the VPN provider. This process ensures that data is protected from interception and that the user’s IP address is masked. However, routing all traffic through the VPN can introduce latency, reduce speeds, and sometimes interfere with access to local or region-specific services.
Split tunneling modifies this behavior by allowing users to define rules for traffic routing. These rules determine which applications, websites, or IP addresses will use the VPN and which will bypass it. The VPN client installed on the user’s device is responsible for enforcing these rules, effectively splitting the traffic into two paths: one encrypted and routed through the VPN, and the other unencrypted and sent through the local network.
This selective approach can reduce congestion within the VPN tunnel and optimize bandwidth usage. It also allows simultaneous access to both secure remote resources and unrestricted local services, which would otherwise be unavailable when fully connected to a VPN.
Types of Split Tunneling
There are two primary configurations that define how split tunneling is implemented, each offering a different level of control and default behavior.
Inverse Split Tunneling operates on a secure-by-default principle. In this configuration, all traffic is automatically routed through the VPN unless explicitly excluded. Users or administrators must specify which applications or destinations can bypass the VPN. This approach is often preferred in professional or enterprise environments where maintaining a high level of default security is important.
Regular Split Tunneling, by contrast, routes traffic through the local network by default. Only selected applications or services are directed through the VPN tunnel. This configuration is typically used to minimize VPN usage while still securing particular activities, such as accessing corporate systems or sensitive accounts.
Both methods rely on defined policies, and the choice between them depends on the user’s priorities, whether those are centered on performance, convenience, or strict data protection.
Performance and Network Efficiency
One of the key reasons users enable split tunneling is to improve overall network performance. When all traffic is forced through a VPN, bandwidth limitations and server congestion can slow down internet speeds, especially for high-demand activities such as video streaming, gaming, or large downloads.
By allowing non-sensitive traffic to bypass the VPN, split tunneling reduces the load on the encrypted tunnel. This leads to faster speeds and lower latency for those activities, while still preserving secure connections for tasks that require privacy. In environments with limited bandwidth, such as remote work setups or mobile networks, this distinction can significantly improve usability.
In addition, split tunneling reduces the processing overhead on the user’s device. Encryption and decryption require system resources, and limiting these processes to only necessary traffic can improve device performance and extend battery life on mobile devices.
Security Considerations
While split tunneling provides clear performance advantages, it introduces important security considerations. Traffic that bypasses the VPN is not encrypted and is therefore exposed to potential monitoring or interception. This includes exposure to internet service providers (ISPs), public Wi-Fi risks, and other network-based threats.
The presence of two simultaneous traffic paths creates a potential vulnerability. If a malicious actor gains access to the unprotected channel, there is a possibility of exploiting the device or intercepting sensitive data if misconfigured. This is particularly relevant in environments where users may not fully understand which applications are transmitting sensitive information.
For organizations, split tunneling can complicate network security policies. Ensuring compliance with data protection standards becomes more challenging when some data flows occur outside the controlled VPN environment. As a result, many enterprises either restrict the use of split tunneling or implement strict policies governing its configuration.
Careful planning and awareness are required to mitigate these risks. Users should ensure that only non-sensitive applications bypass the VPN and that security software, such as firewalls and antivirus tools, is active and properly configured.
Use Cases and Practical Applications
Split tunneling is widely used in both personal and professional contexts due to its adaptability. In corporate environments, it is often deployed to allow employees to access internal systems securely via the VPN while maintaining direct access to local resources such as printers, shared drives, or region-specific services. This reduces unnecessary strain on corporate VPN infrastructure and improves efficiency for remote workers.
For individual users, split tunneling is particularly useful when engaging in activities that require speed and low latency. Streaming services, online gaming, and local browsing are often routed outside the VPN to maintain optimal performance. At the same time, sensitive activities such as online banking, secure communications, or access to restricted content can still benefit from the privacy of the VPN tunnel.
Another practical application involves accessing geographically restricted content. Users may choose to route browser traffic through a VPN server in another region while allowing other applications, such as local services or software updates, to function normally through their standard internet connection.
Setting Up Split Tunneling
The process of configuring split tunneling depends on the VPN provider and the device being used. Most modern VPN applications include built-in options that allow users to define routing rules through a graphical interface. These settings typically provide options to include or exclude specific applications, websites, or IP addresses from the VPN tunnel.
In more advanced setups, particularly within enterprise environments, split tunneling may be configured at the network or router level. This requires a deeper understanding of networking concepts such as IP routing, subnetting, and firewall rules. Administrators often use centralized management tools to enforce consistent policies across multiple users and devices.
It is important to verify configurations after setup to ensure that traffic is being routed as intended. Many VPN applications offer diagnostic tools or connection logs that help users confirm whether specific data is passing through the encrypted tunnel or the local network.
Conclusion
Split tunneling is a practical feature that enhances the usability of VPNs by allowing selective traffic routing. It supports a balanced approach to internet usage, combining the benefits of secure communication with improved performance and accessibility. However, this flexibility comes with inherent trade-offs, particularly in terms of security exposure for non-encrypted traffic.
Understanding how split tunneling functions and how to configure it correctly is essential for making effective use of the feature. Whether applied in a business or personal context, careful consideration of what data requires protection and what can safely bypass the VPN will determine its overall effectiveness.